Next Generation Data Protection
Cyber Reliant Data Protection ensures classified and sensitive data remains protected in the file system of endpoint devices and is an integral component of a comprehensive data security strategy in both connected or unconnected environments.
DATA ALCHEMY
Through our unique process of encryption, data shredding, secure storage and authorized file reconstitution, the data undergoes a transformation process that changes the properties of the data – an approach we call Data Alchemy™

The Data Alchemy process of file level encryption, data shredding, dispersal, and storage renders your data completely unusable and unrecoverable to anyone but the authorized user. When the authorized user access their data, the application retrieves and recombines the original data.
Cyber Reliant’s security always stays with the data even in the event of a breach, endpoint compromise or application vulnerability.
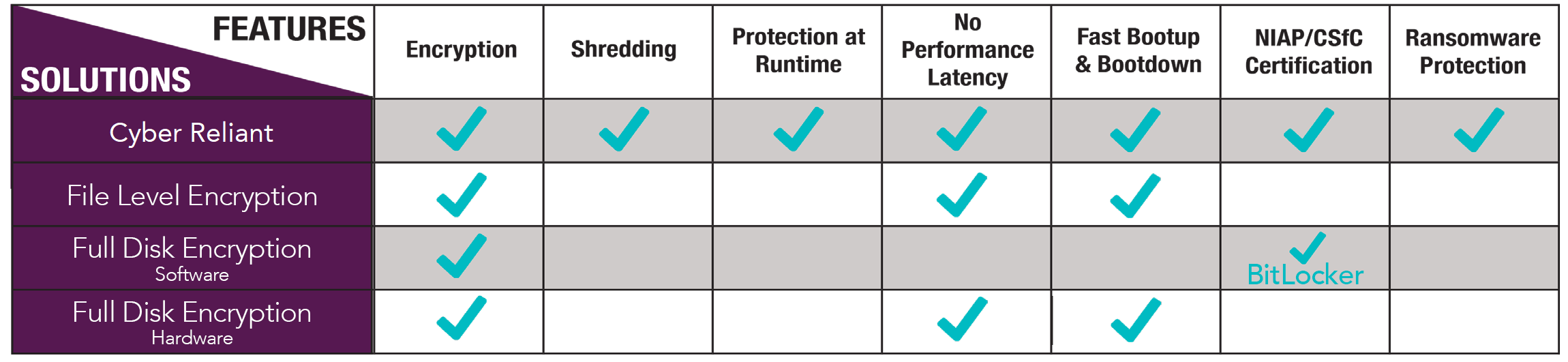
Current Data Protection Solutions Are Not Working
Anti-Malware software will not catch all variations.
Existing security approaches are not sufficient to protect data from ransomware.
Trusted boot-up software alone will not prevent ransomware infection.
Most devices are not up to latest OS patch levels leaving them exposed.
Data at Rest
Cyber Reliant’s advanced data protection encrypts and shreds personal and critical data including PHI, PII, and PAN data, ensuring it remains secure on any device or cloud storage. Cyber Reliant delivers peace of mind to companies that sensitive information and critical data is protected, even in the event of a breach.
Data in Transit
Cyber Reliant’s unique shredding technology works with a three-pronged approach to offer next generation protection for data-in-transit. Using a secure P2PE channel, file shreds are multicasted from the PoS System to the Data Center, where they are reconstituted and tokenized. Data intercepted at any point in its transmission remains useless.
